Subject:Advanced Computer
Networks
Instructor :Bhaskaran Raman
Scribe: Srinivasa Rao Myla srmyla@cse.iitk.ac.in
Lecture No:8
In a network
environment there are many types of senders
with different sending speed.
congestion control can be done by the sender(eg: tcp)
or by the router's(eg:fair queuing).
Fair Queuing:-
It deals with
1. bandwidth allocation.ie among packets send by the
different users which packet hash to choosen so that each
sender will get a fair fraction of bandwidth.
2. how to allocate buffer space fairly among different sender's.
Buffer Space Allocation:
The objective of of any router is to give for
each sender an equal amount of buffer size.
router performs fair queuing by giving equal amount of buffer
space to each sender.
The sender can be identified as
1.source machine .ie buffur space can be allocated per souce machine.
2.destination machine ie buffer space is allocated per one
desination machine.
3.souce machine and destination machine pair.ie buffer space is
allocated per one source and destination pair .
4. individual process based identification.
Advantages:
1.one sender can not can not be domonated by the
other.
2. in this approach the most agressive sender may
lost it's packets.
Disadvantages:
1. Sender's may send their packets with the name of other senders.
2.If one sender is idle and other is sending very repidly then it may
loss packets even if there is an empty space int
the buffur.
One possible correction will be using the empty buffur
space of sender's and if packet's of original sender's come
then the packet's of fast transmitting sender's will be deleted.
Bandwidth allocation:
Bandwidth can be fairly allocated by sending packets of each sender.In
roundrobin fashion.
This may not work if packets are of variable length.
The ideal solution is using bitwise roundrobin.Since it is very
tedious it can not be implemnted because sending one bit per
packet wastes network resources.
So this algorithm is simulated by keeping track of
finishtime.credit will be given to the sender's which
used less Bandwidth.
According to credit of each sender the router will decide which
packet to be send.
When router router received a packet from highly
credited sender while is sending packet of another sender.It may
preempt process or does not preempt the process .
Nonpreemption makes the reouter unfair.
Preemption adds the extra overhead of resending the
preempted packet.
The disadvantage of this approach the router must keep track of
the information of size of the bytes it has sent
and each time a packet has to be sent it must find which sender is
to be choosen by comparing the bytes sofar sent
which is called perpacket over head.
To address this problem Deficit round robin is implemented using Heap
datastructure which can give minimum element in O(log(n)) time.
Congestion Control In TCP:
TCP is a connection oriented protocal which promises
ordered and reliable delivery of messages to apllication system.
It keep track of two windows one is receiver
window whose size is the no of bytes handled by the receiver
.It specifies this number when connection is established.
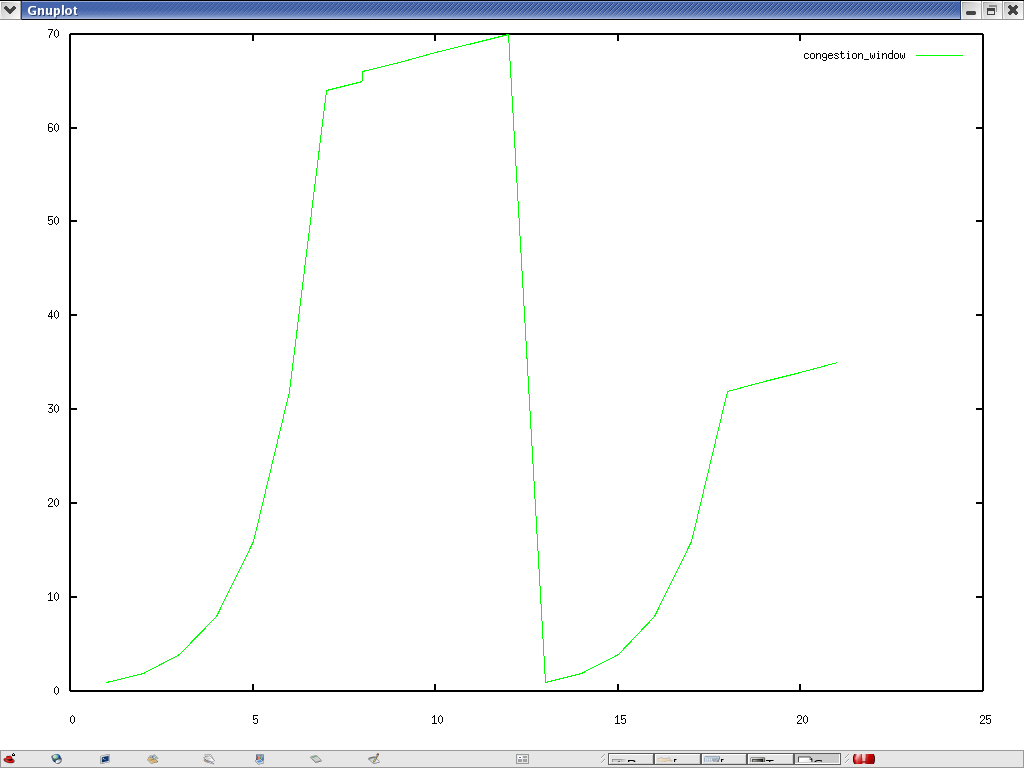
Another window is congestion window which is initially
equal to the maximum size of segment.It contains another variable called
ssthreshold which commly 64k initially.
Initally it sends one segment on if it is acknowldged in time It will
double this .And the process is continued until either
receiver window size is reached or threshold value is reahed.
When it reaches threshold value it increses leniarly it's congestion
window. this is called slow start.
When a timeout occurs it reset's it's congestion window to
one.and sets ssthreshold to half of the previous congestion window
size.
When congestion occurs all the sender's set their window size to one.
At a sudden underusing the network resources.
The remedy for this is Fast retransmit.
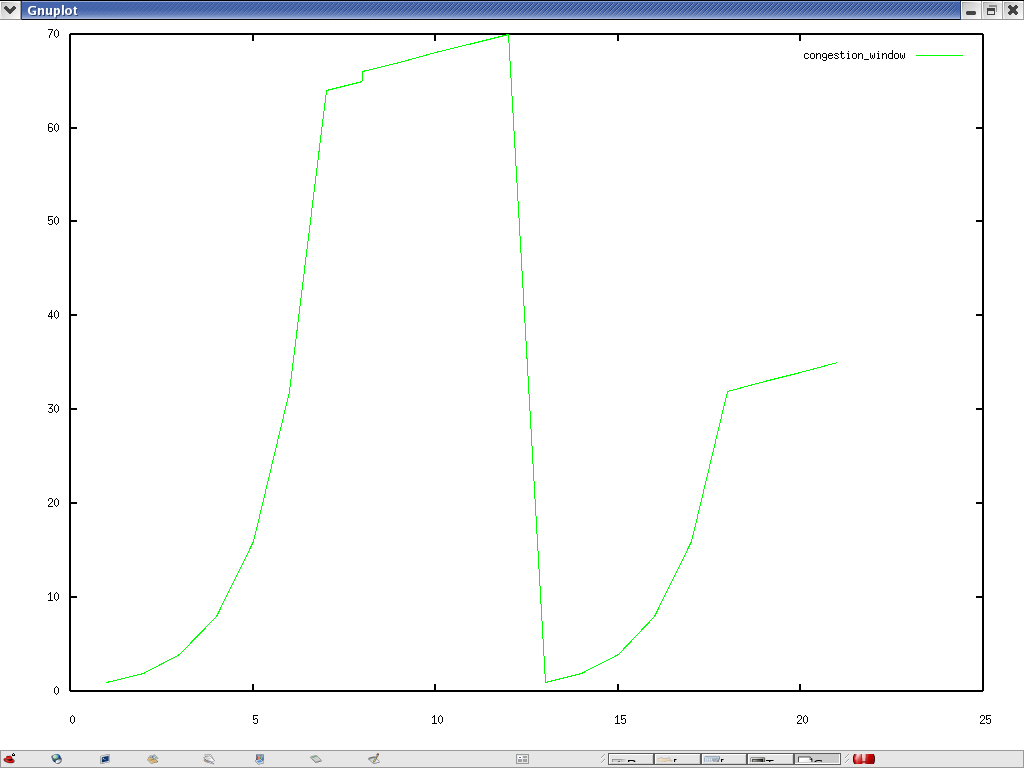
GRAPH OF CONGESTION WINDOW SIZE (Y) VS TRANSMISSION NUMBER (X)
Fast Retransmit:
Since TCP does not know whether a duplicate ACK is caused by
a lost segment or just a reordering of segments, it waits for a small
number of duplicate ACKs to be received.It is assumed that if there is
just a reordering of the segments, there will be only one or two
duplicate ACKs before the reordered segment is processed, which will
then generate a new ACK.If three or more duplicate ACKs are received in
a row, it is a strong indication that a segment has been lost.TCP then
performs a retransmission of what appears to be the missing segment,
without waiting for a retransmission timer to expire.
Fast Recovery:
After fast retransmit sends what appears to be the missing
segment,congestion avoidance, but not slow start is performed. This is
the fast recovery algorithm.
It is an improvement that allows high throughput under moderate
congestion,especially for large windows.
The reason for not performing slow start in this case is that the
receipt of the duplicate ACKs tells TCP more than just a packet has been
lost.Since the receiver can only generate the duplicate ACK when another
segment is received, that segment has left the network and is in the
receiver's buffer.
That is, there is still data flowing between the two ends, and TCP does
not want to reduce the flow abruptly by going into slow start.
The fast retransmit and fast recovery algorithms are usually
implemented together as follows.
1. When the third duplicate ACK in a row is received, set ssthresh to
one-half the current congestion window,cwnd, but no less than two
segments. Retransmit the missing segment. Set cwnd to ssthresh plus 3
times the segment size. This inflates the congestion window by the
number of segments that have left the network and which the other end
has cached (3).
2. Each time another duplicate ACK arrives, increment cwnd by the
segment size. This inflates the congestion window for the additional
segment that has left the network. Transmit a packet, if allowed by the
new value of cwnd.
3. When the next ACK arrives that acknowledges new data, set cwndto
ssthresh (the value set in step 1). This ACK should be the
acknowledgment of the retransmission from step 1, one round-trip time
after the retransmission. Additionally, this ACK should acknowledge all
the intermediate segments sent between the lostpacket and the receipt of
the first duplicate ACK. This step iscongestion avoidance, since TCP is
down to one-half the rate it was at when the packet was lost.
references:
Bhaskaran Raman "Lecture
07 slides"
Bhaskaran Raman "Lecture
08 Siledes"
[Nag87] John B. Nagle, "On
Packet Switches with Infinite Storage", IEEE Transactions
on Communication, 35 (4), Apr1987,pp.435-438.
[DKS89] Alan Demers, Srinivasan Keshav, and Scott Shenker, "Analysis
and Simulation of a Fair Queueing Algorithm", ACM SIGCOMM, Sep
1989.
[Jac88] Van Jacobson, "Congestion
Avoidance and Control", ACM SIGCOMM, 1988.